Majority of organizations are already deep in their DevOps maturity. Most researches are showing over 40% that adopted the process, and are moving towards automated processes, shift-left, and fast delivery of value to customers.
With that in mind, these organizations that span across different verticals from automotive, financial industries, gaming industries, and many more, need to not only deliver high quality code, but also in many cases meet and comply with specific standards and regulations.

If to only focus on the above compliances, teams must bake into their CI/CD pipelines the scanning against such standards, and ensure that they keep up with modifications that are constantly happening across these.
In addition to the above, there are also very important and critical compliances like Autosar (automotive open system architecture), OWASP (top security vulnerabilities), CERT, CWE, PCI and others.
When dealing with smaller teams, managing the code safety and compliance might be easier, however, when you are 1 squad within a bigger DevOps organization, this requires better governance and control. Keeping up with code changes, merges into different branches, while running continuous testing suites, performing code reviews, and SCA (static code analysis) becomes quite challenging.
Building the Perfect Mix : Safety and Compliance together with Code Standards Adherence
To obtain the right mix, continuously, teams must strategically plan their pipeline in a way that democratizes both continuous functional testing, non-functional testing together with the entire sets of compliances and code standards quality assurance.
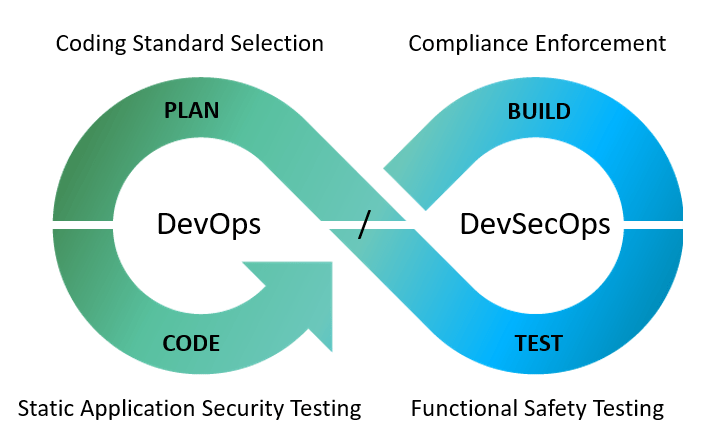
If to analyze the above famous DevOps lifecycle diagram, teams can put the proper activities in the right phases of their cycle to cover all of their required goals.
If to look into an example, using an open-source GPS tracing repository , this project has various modules, and quite a lot of Java classes. Ensuring that the code adheres to the proper Java coding standards, as well as does not violate any of the OWASP items, continuously and from CI is not an easy task.
In the below screenshots, you can see that by running a simple Maven SCA job within CI as a batch project upon each code change, can easily generate a comprehensive report (In my case, I am using Klocwork SCA tool):
“kwmaven clean install compile -Dmaven.test.skip=true”
As soon as I run from the project folder the above command, a full build and scan are being performed on the entire code base, using specific compliance modules that I predefined. The developer receives at the end of his Jenkins job a detailed report and can also login to the KW dashboard to review each and every issue or violation (below is a snapshot of the post build report).

In the above case, I was using Java, and was configuring the below sets of compliance coverage to use for the scanning. Obviously, if I was to cover an app from the automotive or other embedded software industry, I could have added an additional taxonomy/ies.

From a process perspective, the developer should follow the process of per each code change, run a build (either using the team CI trigger, or his own local CI. Once he receives a clear report without critical issues surrounding safety, security, and other code quality standards, he can pass his changes toward the next phase of integration testing, functional regression testing and pre-production activities.
It is clear that such code scanning and quality activities, must be filtered properly to avoid redundant noise, false negatives, etc. This is why, relying on SCA tools that can grant the developers the option to filter by severity, modules, configurations and compliances, allows getting the job done while not overwhelming them with irrelevant feedback.

In the above Klocwork zone within Eclipse (or IntelliJ), users could filter through the relevant columns the issues by Severity and more.
To summarize this post: Teams especially within Agile and DevOps practices can enjoy both types of quality gates by employing SCA tools together with coding standards under the same source base, and once these activities generated Green lights, they can allow testing teams to run their jobs with higher confidence.
In most organizations, testing teams are requiring as a pre-requisite to starting their regression an SCA audit report showing that no major issues were detected within the build cycle.
Keep in mind that the above process and tools is 100% automated, and runs within CI which means, ever for large code bases, this is a few minutes of scanning to get to the quality gate with a peace of mind.

