Gust Blog by: Kanika Vatsyayan is Vice-President – Delivery and Operations at BugRaptors
Over the years, Cyber Security has become a highly sensitive and significant aspect of the IT industry. And it is very natural with hackers leaning on some more advanced approaches to breach public and private networks inspecting the personal information of various organizations.
Most importantly, these cyber-attacks have the potential to feed on business data from any small or large organization using high-end technology to attack digital systems. As per the reports by weforum, approximately $5.2 trillion worth of data would be put at stake because of cyber-attacks from 2019 to 2023.
However, software testing has emerged to be a practice that has helped streamline the cybersecurity factor restricting hacking and diminishing the chances of any threat to data. In other words, software security testing services has turned to be a trusted shield against cyber-attacks and therefore has gained extensive popularity amongst the IT sector.
Importance of Software Testing
With past incidences like the WannaCry ransomware attack of 2017 and the Yahoo breach of 2013, organizations are at constant threat of cyber breaches, deploying a perfect software testing strategy should be an ideal agenda to keep things protected. However, the limited propagation has made security testing an even more complex process to understand.
Above all, there exists a significant irony in the current approach towards software testing for cybersecurity as the present focus of the development enthusiasts is centered around the new development practices. This cuts the scope of improvement for already released technologies and makes them more vulnerable to hacking due to major security gaps.
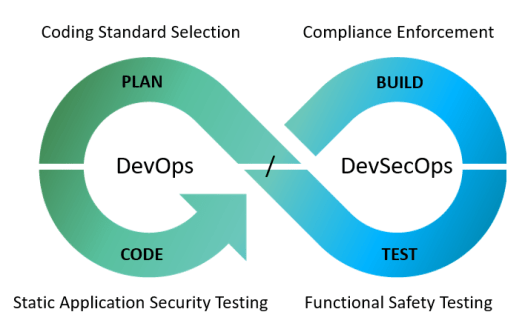
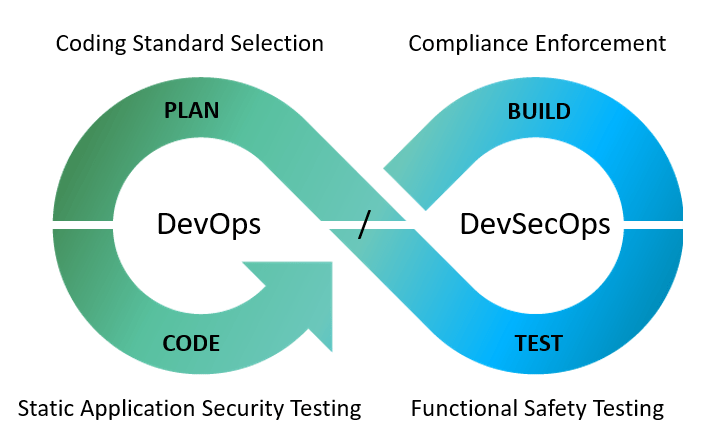
Thus, there is an immediate need to realize the current circumstances and make continuous software testing and DevOps an essential part of the organization’s development practices to improve the entire working propaganda. However, the process needs companies to immediately locate software testing professionals to help with planning the cybersecurity initiatives while driving quality throughout the project pipeline.
Also, the adoption of security testing services would not only aid the security process against unexpected cyber-attacks to industries like healthcare, finance, banking, etc. while improving the entire development design. In a nutshell, the right approach towards software testing could help drive a mature security practice that will run through different stages of the development lifecycle while aligning with cybersecurity objectives.

Penetration Testing & Its Importance For Cyber Security
Over the years, different surveys have revealed that 75 percent of cyber-attacks happen due to insecure code that makes the application unstable. Also, the shift of all the operational processes, as well as day to day tasks to third party applications that have access to global user data, have become the prime spot for cyber attackers.
Therefore, it is necessary that your developers, as well as security testing service provider in India, both aim at improving the source code quality for any tasks that involve the use of data. However, the process to overcome any such code issues require correct implementation of the techniques like penetration testing as it works on how the code connects with the application.
Penetration testing is a technique that highly resembles a cyber-attack or actually an intentional cyber-attack made on the application to identify all the system vulnerabilities. Moreover, penetration testing is a highly effective practice that helps meet the goals related to web application security as it helps to improve the Web Application Firewall or WAF protection.
Intelligent System Security Checks
Penetration testing is more of a test design arrangement made to work on security against any attempt made on hacking. Even the tools used during penetration testing are made to replicate the cyber-attacks with the objective of getting over any system vulnerabilities.
Underline Weak Segments
Another significant aspect of using the penetration testing approach is to identify weak links within the software code. The practice improves the scope for protecting the personal user data, card details, or any transactional record that might be at threat. In short, penetration testing works by analyzing the security vulnerabilities of the system and use them in strengthening the system structure against possible cyber threats.
Added Network Security
Penetration testing is a powerful technique that could help developers and software testers to work on improving the high-speed internet like 5G network security as well as applications running on the network. When implemented through a dynamic approach, penetration testing could help the users to identify any potential vulnerabilities related to the system for preventing any chances of attack. Also, the security-related information can be used to work on compliance goals and plan the security response time to make system protection more definite.
The Crux: Planning Cyber Security With Software Testing
Though penetration testing is a highly efficient software testing practice that is made to simplify the test operations related to cybersecurity, running through other dimensions of testing could help make things better.
For instance, pen testers could consider escalating their cybersecurity initiatives by using advanced cyber penetration techniques. This would not only help make the system more secure but have a complete idea of the likely cyber-attacks that could be planned in the near future. Such arrangement allows tracking of methods that can be imposed by attackers and therefore can be used to prevent any hacking incidents.
All in all, working on the cybersecurity component of software testing is a sophisticated practice that needs testers to analyze all the aspects of the technical landscape. It is not only made to expose potential attacks before they occur but rather uses a similar set of tools and approaches that can be used by hackers. Furthermore, it cuts off the chances of any security compromises that may happen with devices running on public networks.
In a nutshell, software testing has redefined the entire concept of cybersecurity, offering solid protection to the user data as well as development companies. Thus, it is crucial that development firms should start recognizing the importance of software security testing services in the organization when they need to put off any prospective threats as it will not only help users to experience the best of the web but development companies to enjoy sustainable growth.
All the best!
Author Bio: Kanika Vatsyayan is Vice-President – Delivery and Operations at BugRaptors who oversees all the quality control and assurance strategies for client engagements. She loves to share her knowledge with others through blogging. Being a voracious blogger, she published countless informative blogs to educate audience about automation and manual testing.