Essentially, Shift-Left is the practice finding defects and preventing them early in software delivery process. This is done by shifting the scanning of defects to improve code quality process to the left of Software Development Life Cycle (SDLC), which is usually composed of four phases of activities: design, develop, test, and release.
Shift-Left also applies to software security testing (SAST). The aspect of shifting left on security is one of a set of capabilities that is the result of higher software delivery and organization performance. According to the 2020 state of DevOps Report published by Puppet Research, high-performing teams spend about 50% less time remediating the security issues than low-performing teams. By better integrating information security (InfoSec) objectives into daily work, teams can achieve higher levels of software delivery performance and build more secure systems with approved compliance standard library and compliance scannable SCA tools.
Production Defects are Costly.
How Does Shift-Left Help Reduce Product Costs?
Production defects are costly, as an identified defect costs about 30 times more than the same defect fixed in development and takes about 5 times longer to resolve. What is more, certain industries — such as embedded software, medical devices, and high-value transactions — experience even higher costs and reputation damage from bugs.
In addition, fixing defects in testing costs about 10 times more than development and takes only about twice the time it would have taken before checking in the code. In waterfall development, it would not present a substantial difference. However, in the continuous integration assembly line methodology, defects found in testing still break the build.
Shifting Left Effectiveness
Shifting left defect detection — from testing and production to developers — is not a new concept. Rather, it becomes more and more critical as software is integrated into more mission-critical systems, IoT devices, and backend enterprise operations. As a result, the cost and impact of production defects increases as well.
When defects are discovered, developers must then find the contributing factors and fix them. In complex production systems, it is not usually caused by a single issue. Instead, it is often a series of factors that interact with one another to cause a defect. This goes for the defects that are found involving security, performance, and availability — all of which are expensive and time-consuming to remedy, and often require some architectural changes. The time required to find the defect, develop a solution, and fully test the fixes are unpredictable — causing delivery dates to be pushed back.
How Effective is Shift Left for Defect Detection and Prevention
The shift left process, optimizes continuous delivery workflows by reducing build pipeline
breakage. It also allows developers to spend less of their time on diagnosing problems and more time on preventing them during development.
In addition, shift left should help enforce more discipline and create awareness of software quality. However, there are also other tools and techniques that can shift-left the defect detection responsibility to the individual developer:
- Desktop Static Code Analysis (SCA)
Static code analysis automatically finds potential defects or security vulnerabilities in the source code prior to running the application. SCA tools — such as Klocwork or Helix QAC — can be light and look primarily at code syntax, or more sophisticated and examine the complex application execution paths. Industries such as automotive, healthcare, and aerospace mandate the use of such tools in the testing and validation phase.
Integrating SCA at the build or CI process improves quality and security. True shift-left requires wide adoption of SCA at the developer’s desktop, scanning and cleaning the code prior to checking in rather than waiting for the build to fail.
- Use Code Frameworks
By using code frameworks, code components, or libraries, both commercial and open source reduces the volume of custom code developed and therefore eliminate defects making their way into the build. Standard “plumbing” tasks – such as complex UI elements, math and analytics algorithms, data mapping, networking, and so on – can be handled by code libraries while developers focus on true business logic code. Properly tested frameworks that are supported commercially or by a vibrant community, proactively shift-left problem detection by not introducing “plumbing” code defects to begin with.
- Developer Side Application Performance Management (APM)
Application performance management solutions provide production performance and failure alerting, which includes analytics designed primarily for production. It’s unusual not to have comprehensive monitoring in place for production applications. Plenty of commercial and open-source solutions are available for different cloud and on-premises environments.
However, they are not built with developers in mind. Lightweight APM tools designed specifically for developers shift-left performance problems and error detection to the developer desktop. Desktop APM — such as XRebel APM for Java and Zend Server developer edition or ZendPHP for PHP – allows developers to proactively optimize code before it enters the integration phase.
- Standardize Environments
Adopting a standard, automatically generated application stack and virtualization or containerization that matches the production environments is another shift-left practice. It shifts a class of errors to the developers’ responsibility by not introducing them to begin with. In the cloud or on-premises, standard application stacks reduce chances of configuration and environment mismatch issues from making their way into the build.
Shifting-Left for Security Prevention
Security should be everyone’s responsibility. So, by shifting the security review process to the “left” or earlier in the SDLC phases requires several changes from traditional information security methods with additionally scanning for security vulnerability. However, that is not a significant deviation from traditional software development methods on closer inspection:
- Get InfoSec Involved in Software Design
The InfoSec team should get involved in the design phase for all projects. When a project design begins, a security review can be added as a gating factor for releasing the design to the development stage. This review process might represent a fundamental change in the development process. However, this change may require developer training.
- Develop Security-Approved Tools
Providing developers with preapproved libraries and toolchains that include input from the InfoSec team can help standardize developer code, and the tools should include a SCA tool — such as Klocwork or Helix QAC — to scan for any security vulnerabilities in the code, such as tainted-data, cross-site scripting, etc.
Using standard code makes it easier for the InfoSec team to help with reviewing it. Standard code also allows automated testing to check that developer is using preapproved libraries. This can help scale the input and influence from InfoSec teams.
- Develop Automated Testing
Building security tests into the automated testing process means that code can be continuously tested at scale without requiring a manual review. Automated testing can identify common security vulnerabilities, and it can be applied uniformly as a part of a continuous integration pipeline or build process. Automated testing does require you to design and develop automated security tests (pre- and post-software releases), both initially and as an on-going effort as new security tests are identified.
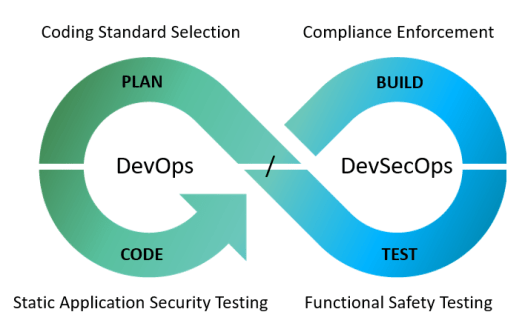
Blending Quality and Security to Create DevSecOps
The traditionally separate relationship of development and security is long overdue for evolution, which has culminated into a cultural shift known as DevSecOps. The name suggests a blending of development, security, and operations. The DevSecOps methodology is built upon the “shift-left” philosophy of integrating cyber-risk management into the architecture and development process from inception. Built-in, not bolted-on, as they say.
With DevSecOps, security is baked into the code from the start, during the early stages of development. Security is part of the architecture, and the application of automated testing throughout the development process drives a higher level of both product quality and DevOps security. Security issues present earlier, making life easier for developers and less costly for management.
This blog was Created by Dzuy Tran, Senior Sales Engineer, Perforce Software
Dzuy Tran has over 30 years of experience in designing and development of Hardware and Software Embedded Systems, RTOS, Mobile Applications and Enterprise Systems. He helps customers when they have technical questions, assists with Proof of Concepts, and conducts demos of the Static Code Analysis tools and help guided customers on DevOps implementation processes and Continuous Integration deployment. Dzuy holds a master’s degree in Computer Science and Computer Engineering from National Technological University.